1. 引言
随着工业技术的发展和工控系统应用的普及,工业生产控制正逐步改变着社会生产方式。工控系统的普及必然带来更高标准的工业安全需求,而对工控系统进行科学合理的脆弱性评估是工控系统安全运行的重要前提保障 [1]。近年来相继出现的毒区病毒、火焰病毒和震网事件等,充分暴露了工控系统安全性差的缺点,对其进行安全评估已经成为国际性难题。工控系统一般划分为三层架构:计划管理层、制造执行层和工业控制层 [2] [3]。
计划管理层主要用于底层信息的汇总和分析,其与制造执行层之间主要进行的安全防护包括身份鉴别、访问控制、检测审计、链路冗余和内容检测等;制造执行层主要包括MES (Manufacturing execution system)服务器或MES数据库等,其与工业控制层之间的防护主要是避免管理层直接对工控层的访问,保证制造执行层对工业控制层的操作唯一性;工业控制层主要由OPC (OLE for process control)服务器、管理终端、PLC (Programmable logic controller)、监控终端等组成。
目前国内外针对工控系统安全的脆弱性评估研究还处于起步阶段,由于工业系统具有复杂度高、灵活性差等特点,使得目前仍然缺少一种成熟的工控系统安全评估方法。从数学建模的角度,刘芳 [4] 提出了一种ISSUE (Information system security evaluation)安全评估方法,并结合安全风险概率预测技术,基于模糊多属性群体决策,将模糊数学、多属性决策和群体决策的理论运用在安全评估中。但该方法需要大量的历史数据作为理论支撑,且评估结果存在不合理的情况;周小锋 [5] 等提出针对ICS (Industrial control system)安全指标的分层计算模型,使用灰色数学模糊聚类方法,增加了评估准确性。但是模糊聚类方法在样本量比较大时,得到聚类结果有一定困难;从网络模型的角度,Vintr等 [6] 基于攻击树模型来评估防护系统的脆弱性,分析了工控系统的网络攻击空间,使用FTA (Fault tree analysis)和ATA (Accident tree analysis)来识别潜在的攻击场景,但该方法不能独立用于识别全部攻击目标;Jha等 [7] 对工控系统进行攻击图建模,为每个原子攻击指派成功发生的概率,利用马尔科夫模型计算攻击者达到攻击目标的可能性。但这个概率值容易受到人为因素的干扰,且该方式实现起来较复杂,使得评估结果缺乏科学性和合理性。从脆弱性指标的评价方法的角度,Sener等 [8] 采用层次分析法来进行地下水系统的脆弱性评估,但该方法的缺点就是评估指标过多时权重无法确定,并且使用特征值和特征向量的计算相对复杂;Stewart等 [9] 采用主成分分析法对多个脆弱性指标进行综合决策,但需要大量样本的支持;从国际标准的角度,美国国家标准与技术研究院(National Institute of Standards and Technology, NIST)发布了一系列指南 [10],重点研究带有复杂网络类型的大型控制系统的深度防御架构及配置方法,包括SP800-82、NIST7176等 [11]。美国国家标准学会(American National Standards Institute, ANSI)制定了ISA99标准 [12],从工业自动化控制系统的安全要求、编程要求、系统级技术要求和组件级技术要求四方面进行安全评估。但这些标准和指南只是提出了一些理论性的概念和知识,缺乏实际的现场可操作性。
结合工控系统的特征和上述脆弱性研究方法的不足,本文提出了一种基于属性攻击图的工控系统脆弱性量化评估方法。首先,提出了两个量化评估指标:漏洞利用难度和漏洞危害性,结合实际工控系统的安全属性,如防御强度、攻击强度、物理损失、信息损失等,制定出一套比较全面的工控系统脆弱性量化指标等级划分标准。其次,利用攻击图来对工控系统的拓扑结构进行建模分析,以研究每条攻击路径的脆弱性为目标,计算攻击过程中每一步的原子攻击期望(该值与漏洞利用难度和漏洞危害性相关),从而得到每条路径的总攻击期望。最后,以锅炉控制系统作为实验对象进行仿真来验证该方法的可行性。相比于刘芳的评估方法,本方法更贴近实际的工业环境,将工艺方面考虑进去,而不是只分析信息安全;相比于周小锋等的模糊聚类,本方法对原始数据的依赖性低,且无需大量样本数据的支撑;相比于国内外标准,本方法具有一定的可操作性;相比于Jha等的方法,本方法与脆弱性标准相结合,因此得到的结果更加科学合理。
2. 属性攻击图模型
2.1. 属性攻击图模型定义
攻击行为建模是实施网络动态威胁分析的理论基础。为避免状态爆炸问题,本文在动态威胁分析模型构建中将采用属性攻击图理论 [13]。目前提出的属性攻击图威胁分析模型仅考虑了系统漏洞引起的威胁转移,但是现实中网络节点间的业务应用存取访问关系同样会造成威胁的转移,因此在动态威胁分析模型构建时融入存取访问关系导致的威胁转移的刻画,具体模型定义如下:
定义1动态威胁属性攻击图(Dynamic Threat Attribute Attack Graph, DT-AAG)可描述为一个4元组:
(1)
其中,C表示威胁转移条件属性集,R表示威胁转移条件属性间的关系集,E表示连接条件属性和关系的边集,p表示威胁转移概率。
1) 威胁转移条件属性集C
(2)
其中
(3)
ID表示前置条件中攻击者的权限,且
。当
时表示攻击者不具有该节点任何权限,当
时表示攻击者具有该节点全部权限,当
时表示攻击者具有该节点全部权限;
表示攻击的源IP;
表示攻击的目标IP;Port表示节点间连接的端口;Vul表示实施攻击的漏洞;Pr表示能够提升攻击者权限的服务访问关系,服务访问关系具体体现为协议。
(4)
表示攻击者实施攻击后获得的权限;
表示获得权限节点的IP地址;
表示攻击利用的端口;
表示实施攻击的漏洞;
表示可提升权限的协议。
2) 威胁转移条件属性间的关系集R
是通过系统漏洞或协议关联主机或服务的关系节点集,其中
和
分别表示漏洞节点和协议节点。
3) 连接条件属性和关系的边集E
(5)
其中,
表示前置条件指向漏洞节点的边;
表示漏洞节点指向后置条件的边;
表示前置条件指向协议的边;
表示协议指向后置条件的边。
4) 威胁转移概率p
威胁转移概率p是指攻击者利用系统漏洞或服务访问关系提升权限达到的威胁转移成功率,其进一步可划分为单步威胁转移概率和综合威胁转移概率,单步威胁转移概率是指攻击者根据
利用系统漏洞Vul或者服务访问关系Pr实施单次威胁转移的成功率;综合威胁转移概率是指多步威胁转移序列造成的威胁转移的成功率。
图1给出了一个典型的DT-AAG攻击图事例,椭圆表示属性攻击图中条件属性,矩形表示威胁转移的关系。攻击者具有网络节点119.188.162.1的
和
,网络节点119.188.162.1与网络节点119.188.162.2通过端口80进行连接,攻击者通过攻击网络节点119.188.162.2的SSH漏洞,获得网络节点119.188.162.2的
。然后攻击者利用网络节点119.188.162.2与网络节点119.188.162.3的ftp协议,获得网络节点119.188.162.3的
。其中虚线框内表示同一节点的相同权限,且攻击者前一步获得的
变为下一步攻击图的
。
2.2. 威胁转移概率p度量方法
威胁转移概率的量化是动态威胁分析模型构建需要解决的关键问题之一。由2.1节可知,威胁转移概率可划分为单步威胁转移概率和多步威胁转移概率。由于网络服务存取关系带来的威胁转移没有攻击权限约束条件,因此本文在单步转移概率度量中默认服务访问关系引起的转移概率值为100%。
1) 单步威胁转移概率度量
在单步威胁转移概率度量方面,本文采纳了CVSS评分标准 [14] 中给出的漏洞可利用性得分ExpSco和漏洞威胁影响得分ImpSco进行威胁转移概率的量化方法。
(6)
(7)
其中,AV表示攻击路径,AC表示攻击复杂度,AU表示身份认证,C表示机密性,I表示完整性,A表示可用性。根据CVE和NVD数据库可查询到CVSS评分标准中需要的漏洞等级评分。
漏洞风险等级Risklevel的计算方法见式(8),其取值范围为[0, 10]。漏洞的攻击成功概率p与Risklevel的函数关系见式(9)。
(8)
(9)
其中,
为漏洞攻击成功概率系数,取值为0.1,以保证漏洞攻击成功概率p的取值范围控制在[0, 1]。
2) 综合威胁转移概率度量
因为前后攻击行为成功概率间不存在明确的关联性,所以可利用贝叶斯概率转移计算方法进行综合威胁转移概率的度量。当攻击者攻击网络系统中的漏洞k时,且攻击漏洞k需要依次攻击
漏洞和利用
存取访问关系获得相应的权限,则漏洞k的多步威胁转移概率计算公式为:
(10)
其中,
表示在多步攻击中,漏洞k被攻击成功概率,
表示漏洞k的单个漏洞被攻击成功概率,
表示漏洞
被攻击成功概率和协议
的威胁转移概率,如图2所示。由于协议的威胁转移概率为100%,因此可将公式表示为:
(11)
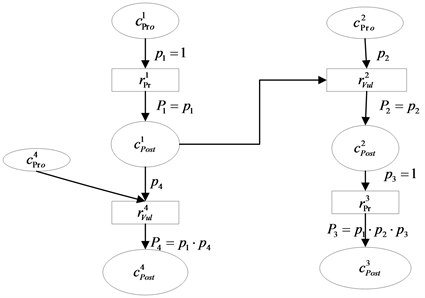
Figure 2. Multi-step attack threat transfer probability map
图2. 多步攻击威胁转移概率图
3. 脆弱性评估指标
为了对工控系统的脆弱性进行全面的量化评估,本文提出两个脆弱性量化指标:漏洞利用难度和漏洞危害性,并进行以下定义。
定义2. 攻击期望(
):漏洞利用难度(
)和漏洞危害性(
)的乘积,记为:
(12)
基于此,对不同攻击路径的攻击期望损失进行综合评价,并用最大的期望损失作为衡量整个工控系统的脆弱性参考指标。
3.1. 防御强度
漏洞利用难度
指利用某一漏洞来实现一次成功攻击的可能性。该指标不仅与防御强度有关,也与攻击强度相关。防御越弱,攻击越强,则漏洞被利用的难度越小。基于工控系统的层次性特点以及其中组件的特点,防御强度主要包括加密、认证、信息屏障、物理屏障,攻击强度主要包括攻击者数量、攻击者的知识水平和威胁频率。
1) 加密:工控系统中传输数据的方式主要有明文传输和密文传输,其中密文传输又包括AES (Advanced encryption standard)加密 [15] 和DES (Data encryption standard)加密 [16]。加密的强度主要可以由密钥长度、破解难度和加减密时间来确定。
2) 认证:工控系统中的组件需要经过认证来鉴别数据的安全性,主要包括数字摘要、数字签名、数字信封和数字证书的四种认证方式,若在某个组件中部署的认证方式越多,则其越安全。其中数字锌粉由于采用双重加密技术来保证只有规定的接收者才能阅读数据,其安全性越高。
3) 信息屏障:主要的防护技术包括防火墙、入侵检测技术和访问控制。其中防火墙又可根据防御能力分为工业防火墙和商业防火墙;入侵检测技术的关键是如何从已知的数据中获得系统的正常行为或有关入侵行为的知识,可以分成模式匹配、神经网络、数据挖掘和数据融合;访问控制根据管理性质和安全级别又可分为基于授权规则的自主管理访问控制(Discretionary access control, DAC)、基于安全级的集中管理强制访问控制(Mandatory accesscontrol, MAC)和基于授权规则的集中管理角色访问控制(Role-based access control, RBAC)。
4) 物理屏障:主要指采取的物理防御手段,包括对外接口数量、组件所处位置、防静电、防火、防雷等。
3.2. 攻击强度
1) 攻击者数量:对某一漏洞利用的人越多,则脆弱性越高。本文参考NIST 7176标准 [17],将攻击者数量分为三个等级:小于100、100~300和大于300。
2) 攻击者知识水平:经验丰富的攻击者显然比首次参与攻击的初学者具有更高的攻击成功概率,据此将知识水平按表1进行分级。
3) 威胁频率:参考《集散控制系统安全评估指南》中对威胁频率的赋值,如表2所示。
4) 漏洞危害性
漏洞危害性
指攻击者利用漏洞对工控系统造成的损失,包括物理损失和信息损失两方面。物理损失与区间相关,组件在整个工控系统中所占的比例或者重要度越大,则可能的物理损失越高;信息损失参考CVSS (Common vulnerability scoring system)标准,从信息机密性、信息完整性和信息可用性来衡量一个漏洞的危害性。
5) 物理损失
工控系统中每个组件根据其扮演的角色不同,具有不同的价值量。例如,一台数据库服务器具有的价值量要比一般的主机具有的价值量高,因为一旦数据库服务器被攻击者控制,许多重要信息将会被泄露、修改或删除。在工控系统根据组件所处的位置分为上机位和下位机,其中上位机包括用户、SCADA (Supervisory control and data acquisition)服务器、工程师站、操作员站、WWW (World wide web)服务站、MES服务器/数据库和OPC服务器/数据库;下位机分为远程终端单元RTU (Remote terminal unit)、可编程逻辑控制器PLC和可编程自动化控制器PAC (Programmableautomation controller) [18]。各个组件价值量的分级参考《集散控制系统安全评估指南》,如表3所示。

Table 3. Classification of component value
表3. 组件价值量分级
6) 信息损失
工控系统组件之间传输的数据或指令的正确性对于整个系统的正常运行起着十分重要的作用,因此利用漏洞来对这些重要信息进行攻击便成为攻击者的一大目标。信息的损失主要体现在机密性、完整性和可用性上。机密性要求信息免受非授权的披露,不被泄露和窃取,涉及到对数据和程序文件读取的控制。完整性要求信息必须是正确和完全的,而且能够免受非授权、意料之外或无意的更改,还要求程序的更改要在特定或授权状态下进行;可用性要求信息在需要时能够及时获得以满足需求,确保用户不受干扰的获得相关系统信息和资源。漏洞被利用后对信息的三种属性的影响分级,如表4所示。
7) 等级划分标准打分
综合漏洞利用难度和漏洞危害性中对各个因素的分级,参考国内外脆弱性标准来对所有因素进行赋值打分 [19]。

Table 4. Classification of three properties
表4. 三种属性影响分级
4. 多指标归一与攻击图生成
4.1. 灰色关联度分析法
对某对象进行评价时,如果仅从单一指标的角度,评价结果存在片面性,因此往往需要将反映被评价对象的多项指标加以汇聚,得到一个综合指标来从整体上反映被评价对象的整体情况,即多指标综合评价方法。
目前存在的综合评价方法包括层次分析法、主成分分析法、TOPSIS (Technique for order preference by similarity to ideal solution)法和灰色关联度分析法等 [20] [21] [22]。其中灰色关联度分析法具有计算简单、数据不必进行归一化、无需大量样本和无需经典的分布规律等特点,此本文采用该方法来对多指标进行综合评价。
灰色关联度分析法的基本原理为:从样本中确定一个理想化的最优样本,以此为参考数列,通过计算各样本序列与参考序列的关联度,对被评价对象做出综合比较和排序。
设有n个被评价对象,每个被评价对象有p个评价指标,则第i个对象描述为:
(13)
具体步骤如下:
1) 确定参考序列,在n个被评价对象中选出各项指标的最优值组成参考序列
。
(14)
2) 计算两集最大差
和最小差
。计算被评价对象序列与最优参考序列间的绝对差列
。
(15)
在此基础上,根据
(16)
(17)
3) 计算关联系数。计算第i个评价对象的第j个指标与最优参考序列间的关联系数
。
(18)
其中,
为分辨系数,用以削弱
过大而使关联系数失真的影响。
4) 计算关联度。各评价对象与参考序列间的关联关系用关联度
表示。
,
(19)
若各指标权重不同,则式(19)表示为:
,
(20)
其中,
为权重,
。
关联系数和关联度能够把影响工控系统脆弱性的各个指标进行多属性决策,采用一个综合量化值来替代多个指标量化值,使得量化结果没有片面性,同时能够从整体上反映脆弱性的大小,关联度越大,则对应的系统脆弱性也越大。
4.2. 攻击图生成算法
攻击图作为一种描述攻击者从攻击起点到攻击目标的所有可视化路径的方法,已经成为分析系统脆弱性的主流评估模型。攻击图G可以表示为
,其中V为图中节点的集合,E为节点之间链路的集合。透过攻击图可以很明确的得到从某一节点到目标节点的所有潜在攻击路径。
本文采用广度优先算法来生成攻击图,并将该算法与量化指标相结合,生成攻击图的同时计算每一步的原子攻击期望。广度优先算法一般用于求解最优值的问题,而且相比于深度优先算法,它可以控制队列的长度,不容易产生堆栈溢出等问题。算法基本步骤为:
步骤1. 根据工控系统的拓扑和组件相关信息建立参数向量;
步骤2. 确定工控系统的初始状态,加入状态队列;
步骤3. 执行循环:当状态队列不为空,则从队列中取出一个节点作为当前节点,并生成该节点可能进行的所有状态转移,得到新的状态节点,如果该节点为新,则加入队列,并计算实现状态转移时的攻击期望,更新攻击图节点和边的信息;
步骤4. 重复执行步骤3,直到队列为空。
在生成攻击图前,需要收集系统的拓扑信息以及其中组件的相关脆弱性信息,以此作为该算法的输入,输出为潜在的攻击路径和每条攻击路径的原子攻击期望。
5. 案例分析
以真实的锅炉控制系统作为实验背景,参考锅炉工艺流程和SCADA系统的一般架构,模拟攻击者通过外网攻击用户并逐步入侵工控系统的过程。实验拓扑如图3所示。
由图3可知,该系统一共包含6个组件,每个组件上的漏洞信息如表5所示。
5.1. 漏洞利用难度量化
对各个漏洞的利用难度进行具体的赋值打分,结果如表6所示。
之后根据灰色关联度分析法对上述指标进行综合评价,其中n为6,p为10。参考序列
为
(21)
最大差
和最小差
分别为:
根据式(5),并取
,则漏洞CVE-1999-0917加密的关联系数为
。
同理可以得到其他漏洞的关联系数。根据各个指标的不同取不同的权重系数,表6中的各个指标依次对应权重为
。之后根据式(21)可以求得各个漏洞的利用难度关联度,如表7所示。

Table 5. Information of component vulnerability
表5. 组件漏洞信息

Table 7. Degree of Vulexp for various vulnerabilities
表7. 各个漏洞的利用难度关联度
5.2. 漏洞危害性量化
参考表6,对漏洞危害的因素进行赋值打分,如表8所示。
同样采用灰色关联度分析法,取对应权重分别为0.7和0.3,可以得到漏洞危害性的关联度,如表9所示。

Table 9. Degree of Vulhaz for various vulnerabilities
表9. 漏洞危害性关联度
5.3. 攻击图生成
对于简单的公式,在计算得到漏洞利用难度和漏洞危害性的量化值后,根据式(20)可以计算每个漏洞的攻击期望,如表10所示。

Table 10. Attexp for various vulnerabilities
表10. 漏洞攻击期望
之后结合图3的拓扑结构和攻击图生成算法,采用Graphviz软件对攻击图进行输出,如图4所示。
图3中,深色椭圆表示攻击者,椭圆内的数字表示漏洞编号,边上的信息包括可利用的漏洞以及对应的漏洞攻击期望。由此可以计算出每条攻击路径的总攻击期望,定义为攻击路径上各个漏洞攻击期望之和,结果如表11所示。
由表11可知,同处于下位机的PLC (IP4)比IP5的重要性更高,攻击IP4能获得更大的收益,虽然IP4的利用难度大于IP5,但其被利用后的危害性更大,这也证明单凭一个指标不能对各个组件的脆弱性进行比较,否则得到的结果正确性不高;操作员站和工程师站的重要性不同,在本案例中操作员站IP3比工程师站IP1重要,主要的影响因素是利用的危害性(利用难度相差不多);此外漏洞CVE-1999-0917的利用价值最大,为0.013,漏洞CVE-2013-0675和CVE-2013-3175的利用价值最小,为0.005,这表明越上层的组件越重要,因为底层的组件被利用后仅仅这一个组件被控制,造成的损失可能是一台PLC的爆炸或崩溃,但若上层的组件被控制,再加上工控系统的组件采用分布控制、集中管理,则可以通过一台上位机向多个底层组件发送错误指令或数据,导致大量的组件爆炸或崩溃,造成的危害更大。
6. 总结
工控系统的安全问题正受到越来越多人的关注,对其进行安全评估刻不容缓。本文在系统地研究工控系统存在的各类脆弱性后,提出了漏洞利用难度和漏洞危害性两个量化评估指标。根据实际工控系统中的工艺流程,结合攻防强度、物理损失和信息损失等方面制定出一套较全面的漏洞等级划分标准,使该标准更贴近工业环境。同时,根据广度优先算法生成攻击图来对工控系统进行建模,最后以实际的锅炉控制系统为背景进行了实验模拟和仿真分析,得到了总攻击期望最大的路径。实验结果表明,该方法综合了工控系统中潜在的安全威胁,考虑了影响脆弱性的各个方面,由此得到的评估结果更加科学合理。
致谢
感谢杨云雪老师的指导。
基金项目
本文受江苏省高等学校大学生创新创业训练计划项目(202012078001Y)资助。
NOTES
*通讯作者。